Key Takeaways
- Convert unnecessary admin accounts to standard users, enforce a least‑privilege model, and keep User Account Control set to Always Notify.
- Prevent privileged users from running MMC with admin rights, from executing command‑prompt, PowerShell, or Windows Script Host scripts, and from editing the Windows registry.
- Block admin users from disabling the Windows Defender firewall and from elevating browsers, email clients, or other applications that could launch malware.
 Quick question. How many Windows administrator accounts exist in your company? Lots of them? Then it’s likely that many of these privileged accounts are used by individuals who don’t need this level of access to perform their role; or who only need privileged access for one or two tasks.
Quick question. How many Windows administrator accounts exist in your company? Lots of them? Then it’s likely that many of these privileged accounts are used by individuals who don’t need this level of access to perform their role; or who only need privileged access for one or two tasks.
The truth is, providing full admin rights to users who aren’t trained as IT system administrators increases security risk and manageability costs and makes it difficult to achieve compliance. This blog briefly presents six simple restrictions that, when combined, will: 1) reduce the likelihood an individual will inadvertently change some administrative settings and require IT assistance to fix the issue; and 2) make it more difficult for an individual to alter or disable certain protections on your endpoints.
For even better protection, your long-term goal should be to change any unnecessary administrator accounts to standard user accounts and employ a least privilege approach.
Six Simple Restrictions
1 – Prevent Users from Changing the UAC Setting
Ivanti advises that all your end-users, including those with admin accounts, employ User Account Control. Microsoft states on its website: “User Account Control (UAC) helps prevent malware from damaging a PC and helps organizations deploy a better-managed desktop.”
It’s advisable that UAC is active on all machines, with the Always Notify setting selected. This is set via group policy. Ivanti Security Controls can prevent administrators from turning off User Account Control.
2 – Prevent Users from Running the MMC with Admin Privileges
Microsoft’s management console (MMC) is a framework that provides end-users with an interface for management and configuration of the operating system. It allows the end-user to load snap-ins. Each snap-in is a tool to manage a particular Windows feature, e.g., the Services snap-in provides a tool to manage Windows services.
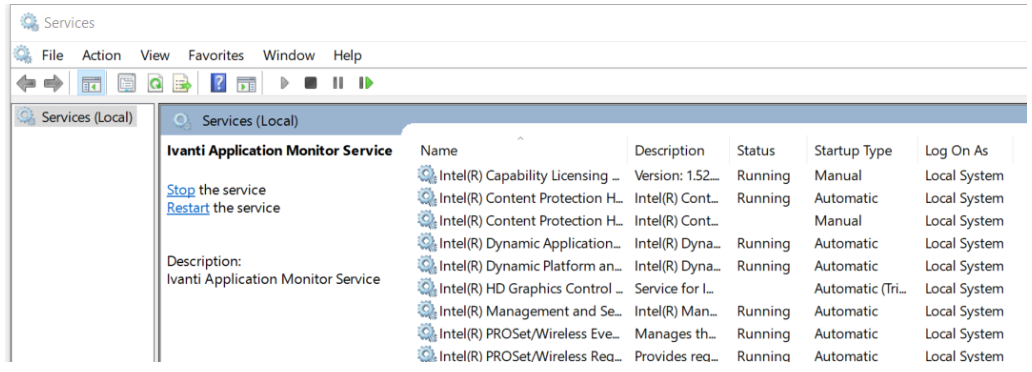
This can be very powerful. For example, in the Services snap-in, an end-user with admin privileges can stop services. If a stopped service was part of your antivirus software, it could disable antivirus scanning on any downloads, increasing the threat from malware. With Ivanti Security Controls, you can prevent end-users with administrator accounts from running the MMC with administrator privileges.
3 – Prevent Users from Running Commands or Scripts with Admin Privileges
Windows supports some alternative ways to interact with the operating system by issuing specific commands via command line interpreters or by executing scripts. The former is used for management purposes and the latter is typically used for automation. The command line interfaces that come with Windows are the Command Prompt and Windows PowerShell. Also included with the operating system is the Windows Script Host that can be used to run scripts in a variety of scripting languages.
Anyone with administrative privileges can execute commands or scripts, and this provides an alternative method in many cases to override the GUI-based restrictions mentioned in this blog. For this reason, the command line interpreters and the Windows Script Host should be restricted. The application-control capabilities in Ivanti Security Controls can help with this.
4 – Prevent Users from Being Able to Edit System Settings in the Registry
The Windows registry is important because it stores vital information about a Windows endpoint and its configuration, as well as information about all application programs that are installed. By offering the ability to directly access and change registry keys, admin privilege allows end-users to navigate around central management policies whenever they choose and change the settings. This access provides another route for users to circumvent many of the protections described in this blog. Ivanti Security Controls can be used to restrict privileged access to the registry or to block access to the registry entirely.
5 – Prevent Users from Disabling or Changing Endpoint Firewall Settings
A firewall is a network-security device that monitors traffic to or from your network and allows or blocks traffic based on a defined set of security rules. Firewalls make it more difficult for malicious software to spread throughout a network.
If you’re using the Windows Defender firewall, then preventing this functionality from being disabled is recommended. You can do this using Ivanti Security Controls.
6 – Prevent Users from Elevating Applications that Could Introduce Malware
End-users with admin privilege can launch any application with elevated privileges. Some of these applications—email and browser applications, for example—can introduce malware to an endpoint. If one of these applications is running with admin privilege, then any child processes spawned containing malware would also run with admin privilege. With Ivanti Security Controls, you can restrict these applications so that they only ever run with standard privileges.
What Next?
Ivanti Security Controls makes it easy to enforce these restrictions right now. Read the full whitepaper to discover how to enforce these six—and a few others, too!