
Microsoft has released updates resolving 101 total vulnerabilities (CVEs), 98 new and 3 revisions to CVEs from November and December of 2022. 11 CVEs are rated as Critical this month. The most urgent of these are one known exploited vulnerability (CVE-2023-21674), one publicly disclosed vulnerability (CVE-2023-21549) and an update to an advisory from December 2022 (ADV220005).
Advisory 220005 (ADV220005) provides “Guidance on Microsoft Signed Drivers Being Used Maliciously”. Microsoft has included a block list in the January 10, 2023, OS updates which blocks the signing certificates that were compromised. Microsoft recommends all customers update to the January 10, 2023 update to ensure they have the most up-to-date block list.
Microsoft has resolved a known exploited vulnerability (CVE-2023-21674) in Windows Advanced Local Procedure Call (ALPC) which could allow an Elevation of Privileges. The vulnerability is rated as Important and affects all Windows OS versions. The vulnerability could allow a browser sandbox escape and the attacker could gain SYSTEM privileges.
Microsoft has resolved a publicly disclosed vulnerability (CVE-2023-21549) in Windows SMB Witness Service which could allow an Elevation of Privileges. To exploit the vulnerability an attacker could execute a specially crated malicious script which executes an RPC call to an RPC host.
This could result in elevation of privilege on the server. The vulnerability is rated as Important and can be exploited over the network without need for user interaction. Public disclosure means enough information regarding this vulnerability has been disclosed publicly giving attackers a head start on reverse engineering the vulnerability to attempt to exploit it.
For January 10, 2023, Patch Tuesday the majority of the risk is in the Windows OS update across all current versions. It is recommended to prioritize the Windows OS updates as a high priority this month.
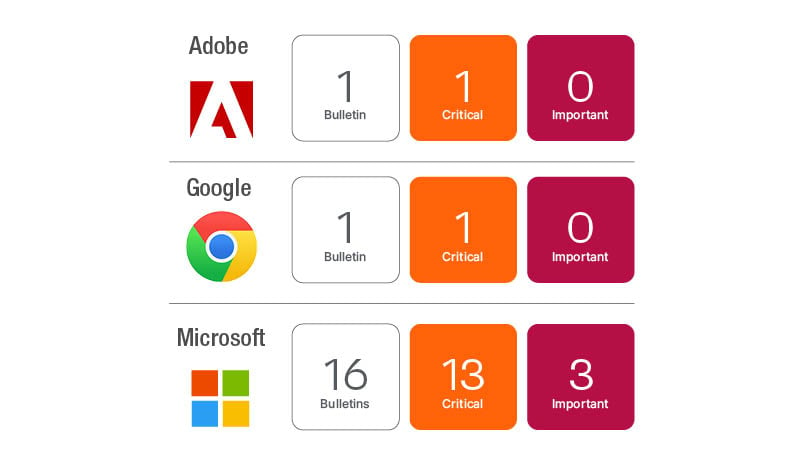
Adobe released updates for Adobe Acrobat and Reader (APSB23-01) that resolve a total of 15 CVEs, 8 of which are rated as Critical. The udpate is a Priority 3, which according to Adobe’s rating system means “This update resolves vulnerabilities in a product that has historically not been a target for attackers. Adobe recommends administrators install the update at their discretion.”
Oracle’s quarterly CPU will be releasing on Tuesday, January 17. Be prepared for updates for all your favorite Oracle products, but more importantly expect updates for Java and additional updates for Java alternatives like Corretto, AdoptOpenJDK, RedHat OpenJDK, Azul Zulu JDK and others. Oracle’s quarterly CPU starts a domino update effect across the Java solutions.
Windows lifecycle update
January 2023 Patch Tuesday is the final extended support update (ESU) for Windows 7, Server 2008 and 2008 R2. Microsoft will be continuing one additional year of ESU support for Server 2008 and Server 2008 R2, but only if it is running in Azure.
January 2023 Patch Tuesday is also the last security update for Windows 8.1.
Windows Server 2012 and 2012 R2 will reach its end date on October 10, 2023. Microsoft will offer ESU support for three years starting from October 11, 2023. More details, including migration guidance and a lifecycle FAQ, can be found on the Server 2012 R2 lifecycle page.
Guidance for Exchange customers about ProxyNotShell and OWASSRF exploits with the recent Play Ransomware attack against Rackspace customers
Microsoft responded to the initial ProxyNotShell exploit with two recommendations. A “URL Rewrite rule” and “Disable Remote Powershell for non-admins”. Microsoft is still recommending the latter disabling of powershell for non-admins as general guidance. The URL Rewrite rule was modified many times between initial release and November 7th. On November 8th, 2022 when the update for Exchange Server was released, Microsoft’s guidance was updated:
Update 11/8/2022
We have now released November 2022 Security Updates for Exchange Server. Please install those (or newer) updates to address vulnerabilities mentioned in this post. Mitigations are no longer recommended.
Rackspace stated the Nov 8th patch had caused performance issues for their hosted Exchange services, so they decided to continue to run with the mitigation. There is a lot of gray area for interpretation of what was the best or right answer, but this event brings up two critical points that I think all organizations should keep in mind.
Mitigations are not permanent fixes. In any case where there is a mitigation option it is meant as a short-term solution but will come with some tradeoffs. Log4J’s mitigation could still be protecting you today if you implemented the guidance specific to solutions in your environment. This would come at the cost of some logging features not being available, but the mitigation would still be effective.
PrintNightmare was a different story. You needed to turn off the print spooler and have no printing ability until the patch was released. In the case of ProxyNotShell and OWASSRF the original mitigation was intended to stop the initial steps used in the ProxyNotShell attack.
It did not account for other exploit methods that could bypass the URL Rewrite Rule mitigations created to mitigate ProxyNotShell, so it was very narrow in scope to prevent the original attack specifically.
In the case of the Play Ransomware attack the mitigations were never intended to stop OWASSRF’s attack method. Be careful how much long-term trust you put into mitigations as they were never intended to be permanent fixes.
Products and technologies have a shelf life. At some point a vendor does need to move beyond a solution as the cost of completely revamping said solution to meet more modern use cases and needs becomes very difficult. Exchange Server is a good example of the dangers of holding onto a technology too long.
Security researchers have stressed some fundamental risks with running Exchange Server. The complexities and difficulties of running an Exchange Server implementation with the level of security that Microsoft can deliver through O365 is really the key tradeoff.
OWASSRF and ProxyNotShell are the most recent, but the 2021 ProxyShell and HAFNIUM exploits were additional examples of high risk of continuing to invest in Exchange Server.
Can an organization run a secure Exchange server instance? Arguably yes, but a sophisticated threat actor with more intimate knowledge of Exchange Server than your organization will continue to find a way to circumvent how effectively you can secure your email services.
To properly assess this risk, you must assume you are competing with the concerted efforts of very knowledgeable adversaries. If you have not accounted for this in your risk assessment, chances are your organization is continuing to run Exchange Server under false assumptions.
