Key Takeaways
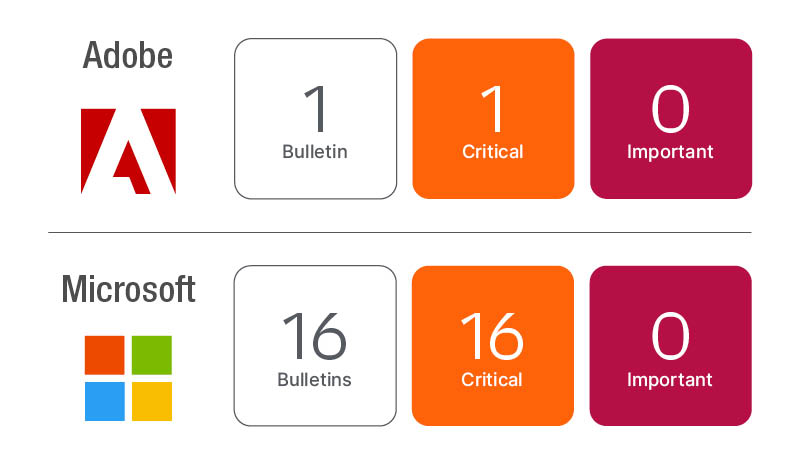
- Microsoft released 89 fixes, including a known exploited zero day in the COM+ Event System (CVE‑2022‑41033). The update also contains 13 Critical CVEs, while Exchange patches still lack fixes for the September zero days (CVE‑2022‑41040 and CVE‑2022‑41082).
- Adobe released an update for Acrobat and Reader that fixes six vulnerabilities, two of which are Critical. Support ends for Acrobat and Reader 2017 Classic, so the product should be removed.
- Oracle’s quarterly CPU arrives on October 18 and will likely trigger Java updates from multiple vendors. A bi‑weekly or weekly update cadence is recommended to keep pace with continuous third‑party patches.

October is Cybersecurity Awareness Month. It is a good month to educate the masses on security related topics in the hopes that the world may shift toward being a little more cyber secure.
For that purpose, I am starting the October Patch Tuesday blog post with one of my favorite cybersecurity tips regarding passwords and will be providing additional cybersecurity tips throughout the blog post:
“Passwords are like underwear: keep them private, make them exotic and change them on a regular basis!”
The October Patch Tuesday lineup is predominantly a Microsoft lineup but includes an update for Adobe Acrobat and Reader (APSB22-46) and is a prelude to the Oracle Quarterly CPU due to release on Tuesday, October 18th.
The Oracle CPU will very likely include an update for Java which will trigger a series of additional Java alternatives to release, so no matter which variation of Java you are using, expect to have updates for them over the next couple of weeks.
Microsoft release
Microsoft resolved a total of 89 unique vulnerabilities (CVEs) for the October Patch Tuesday update. This months CVEs include one zero day vulnerability and two public disclosures. There are 13 Critical CVEs and 76 Important CVEs. Five of the CVEs that affect Exchange Server are re-released from August to resolve a known issue.
The Exchange Server update does NOT contain fixes for the zero day vulnerabilities reported on September 29, 2022 (CVE-2022-41040 and CVE-2022-41082). Microsoft advises it will release the additional Exchange fixes when they are ready, but does provide mitigates in a blog post.
Zero day vulnerability
Microsoft has resolved a vulnerability in Windows COM+ Event System Service that could allow an Escalation of Privilege (CVE-2022-41033). The vulnerability was reported to Microsoft by an anonymous source and has been confirmed to be exploited increasing the urgency to get this vulnerability remediated.
The vulnerability affects all Windows OS versions including Windows 7 and Server 2008\2008 R2. Microsoft rates the vulnerability as Important, but that severity does not adequately weigh the fact that it is known to be exploited in the wild.
Cybersecurity tip
A risk-based vulnerability management approach to prioritization takes CVSS and vendor severity into account, but also includes risk indicators like public disclosure, known exploited, ties to malware and ransomware, and if the vulnerability is trending (being seen often in attacks).
Publicly disclosed vulnerabilities
Microsoft has re-released a fix for a vulnerability on Microsoft Exchange that could allow Information Disclosure (CVE-2022-30134). This is one of a set of five CVEs that were originally released in August.
These CVEs do require additional actions to protect against these vulnerabilities. This requires turning on Windows Extended Protection, which is where the known issue comes in.
The August Exchange Server update introduce an issue where Outlook Probes stopped functioning properly when extended protection was turned on and the August update was applied. The re-release resolves this known issue.
Microsoft resolved a vulnerability in Microsoft Office for Mac that could allow for Information Disclosure. The vulnerability is rated as Important.
A publicly disclosed vulnerability is when information is reveled publicly and could give threat actors an advantage to exploit the vulnerability before the vendor can release a fix. In this case the CVE exploit code maturity is listed as unproven, so the exposure may not be too serious.
Adobe Acrobat and Reader release
Adobe has released an update for Adobe Acrobat and Reader (APSB22-46) resolving six unique vulnerabilities including two Critical CVEs that could allow arbitrary code execution.
Another important note regarding Adobe this month is the end of support for Adobe Acrobat 2017 Classic and Acrobat Reader 2017 Classic. Adobe will no longer be providing technical support, product or security updates for this version of Adobe Acrobat and Reader.
Cybersecurity tip
End of Life software posses a security risk to your environment. The longer an EoL’ed software title exists in your environment the great the increase in risk and potential costs. End of Life’d software can present a supportability risk. If the software fails, the vendor is not obligated to provide support or fix the issue.
From a risk perspective EoL software titles become targets. Regulatory requirements specify that software used must be supported and by failing to maintain supported software a business could face fines in the case of a failed audit or security breach.
Oracle quarterly CPU release
Oracle releases updates on a quarterly basis in the first month of each quarter on the Tuesday closes to the 17th. For October this means Tuesday the 18th. As mentioned previously, there is a domino effect when Oracle Java release. Several alternative Java solutions update shortly after Oracle release the latest Java updates.
Azul Platform Core, RedHat OpenJDK, Amazon Corretto and AdoptOpenJDK will all update over the course of the next few weeks to resolve many of the vulnerabilities that Oracle will release in their next Java update. Google Chrome is another common example as there are many Chrome Frame based browsers including Microsoft Edge (Chromium).
Cybersecurity tip
Most software vendors are on a continuous release cycle. This means they release software as soon as it is available. While Microsoft’s Patch Tuesday cadence has become a well-known starting point for most organizations to begin update maintenance, it is important to keep a continuous cycle of vulnerability assessment and prioritization.
Establishing a bi-weekly or weekly cadence for updating end user systems is recommended to keep up with the continuous cycle of third-party security updates that are introduced especially high-profile targets like browsers.
