Key Takeaways
- Microsoft’s Patch Tuesday fixes 75 vulnerabilities, including a critical IE zero day (CVE‑2019‑1429) already seen in the wild and an Excel flaw (CVE‑2019‑1457). Apply both updates immediately to mitigate elevated risk.
- Google Chrome’s November update (78.0.3904.87) resolves a use after free zero day (CVE‑2019‑13720) and two additional flaws. Upgrade browsers without delay to close the recent wave of exploit activity.
- Servicing Stack Updates were released for all Windows versions except 10 1703 and should be tested lightly this month before large scale rollout. Windows 10 version 1803 receives its final security update for Home, Pro and Pro for Workstations, while Windows 7 and Server 2008/2008 R2 reach end of life on Jan 8 2020, with extended security options available.
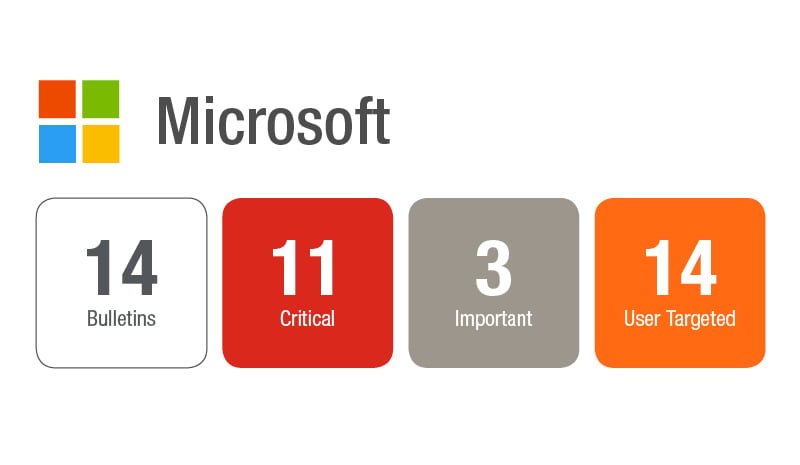
Microsoft released updates for Microsoft Windows, Internet Explorer and Edge browsers, Microsoft Office and Office 365, Exchange Server, ChakraCore, Secure Boot, Visual Studio, and Azure Stack. Microsoft has resolved a total of 75 vulnerabilities that include a Zero Day IE vulnerability (CVE-2019-1429) and an Excel vulnerability (CVE-2019-1457) that has been publicly disclosed. The most excitement from non-Microsoft updates currently was the recent Google Chrome Zero Day (CVE-2019-13720). Adobe has released security updates for Animate CC, Illustrator CC, Media Encoder, and Bridge CC resolving a total of 11 vulnerabilities. All are rated as priority 3. There are some Windows End of Life dates that you should be aware of bot this month and coming in January and some additional details on extended support for Windows 7 and Server 2008\2008 R2 from a blog post in November that discuss how to get access and ensure your systems are prepared for extended support if you are continuing on.
As you may recall in October Microsoft had released Servicing Stack Updates across the board. Well for November they released updated SSUs for all but Windows 10 1703. Update services in Windows will at some point become a pre-requisite for future updates on affected systems. Microsoft usually releases the SSU at least a couple months before the changes will be fully in effect. The shortest we have observed an SSU release to being required for future updates has been two months. Maybe take a conservative approach this month and do some light testing and see what happens in December before going too crazy with your SSU rollout.
Microsoft has resolved a Critical vulnerability (CVE-2019-1429) in Internet Explorer that could allow for an attacker to execute code remotely. An attacker could execute arbitrary code in the context of the current user if they corrupt memory in a specific way. The vulnerability only gains them equal access to the current user so proper privilege management would mitigate the attackers ability to take full control of the system without using additional elevation of privilege exploits. For attack vectors an attacker could craft a website or embed an Active X control marked with “safe for initialization” in an application or Office Document that hosts the IE rendering engine. Security training on common phishing and user targeted attack methods could further reduce the risk of this vulnerability being exploited, but as it is already being exploited in the wild it is highly recommended to get the patch rolled out quickly to resolve the vulnerability completely.
Microsoft has resolved a publicly disclosed vulnerability (CVE-2019-1457) in Office Excel that could bypass security features. An attacker could embed a control in an Excel worksheet that specifies a macro should be run. Whatever is executed in the macro that was triggered by bypassing the security settings of Excel would be the real risk of this vulnerability. This vulnerability is not currently being exploited in the wild, but since it has been publicly disclosed threat actors have had a jump start on being able to develop an exploit to take advantage of the CVE. This puts it at higher risk of exploitation.
There seem to be a string of browser exploits recently. In September there was an IE Zero Day (CVE-2019-1367) followed by a Google Chrome Zero Day that released on November 1st and then the November Patch Tuesday IE Zero Day (CVE-2019-1429). Patch those browsers! The Chrome update (78.0.3904.87) resolved two vulnerabilities, one of which was the aforementioned CVE-2019-13720. The vulnerability is a use-after-free memory corruption exploit that allows an attacker to execute malicious code.
Windows 10 branch 1803 for customers running on Home, Pro and Pro for Workstations editions has received its final security update today. If you are running on Enterprise and Education editions you have until November 10th, 2020 to transition yet. The next Windows End of Life date will be January 8th when Windows 7 and Server 2008 and 2008 R2 reach their inevitable end. Or is it the end? For some there may be ways to carry on with updates for these platforms for a fee or in some cases for free. Check out the details in Microsoft’s October 17th blog post on how to get extended security updates for eligible Windows devices.
