Key Takeaways
- Derived credentials convert a physical smart card’s certificate into a mobile digital certificate, enabling passwordless multi‑factor authentication for iOS and Android devices.
- MobileIron PIV‑D Manager integrates with PKI systems to provision, encrypt to FIPS 140‑2 standards, and manage these credentials, supporting FIPS 201, NIST SP 800‑157 and HSPD‑12.
- Federal agencies such as FEMA and DISA have deployed the solution to tens of thousands of devices.
- The deployment provides secure single sign‑on, S/MIME and advances Zero Sign‑On within a zero‑trust framework.
*This post originally appeared on the MobileIron blog prior to the acquisition in December 2020, when MobileIron became part of Ivanti.
MobileIron has been an innovator in the modern identity and mobile device management space since we shipped our first product in 2009. Since that time, MobileIron has worked with government agencies, the National Institute of Standards and Technology (NIST), and industry partners to pioneer derived credentials on mobile devices, allowing government entities and regulated industry customers to evolve traditional desktop security models to mobile.
What is a derived credential?
If you aren't in the government space or a highly regulated industry you’ve probably never heard of derived credentials. Many government agencies and regulated industries have standardized on using smart cards to log into traditional enterprise workstations like laptops, desktops, and enterprise web services. An employee inserts their smart card into a reader embedded on a workstation and enters a pin to log into the device and enterprise web services. This authentication method replaces username and passwords and provides a second factor of authentication, because the smart card is something the user has and the pin is something only they know (these rules are described in the FIPS 201-2 definition of multifactor authentication).
Derived credentials allow organizations that are using smart cards for authentication to easily extend this technology to mobile devices, providing strong, password-less authentication to the most sensitive of resources. Derived credentials are a mobile-focused evolution of smart card identity because the credentials are created or “derived” from the physical smart card. The end user securely authenticates to a portal using their physical smart card on an enterprise workstation. Then, using the information on the smart card, a mobile-friendly soft token is created and stored in a secure enclave on the mobile device as a digital certificate. The derived digital certificate is tied to a certificate on the smart card for revocation and validity. These certificates can be used for secure authentication to enterprise web services, to sign emails and documents, and to encrypt messages on mobile devices.
What kind of smart cards are out there?
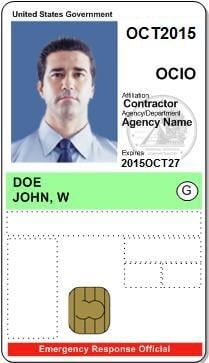
U.S. civilian government agencies have standardized on smart cards called Personal Identity Verification (PIV) while the U.S. Military and Defense agencies have standardized on the Common Access Card (CAC). These types of smart cards and underlying technologies differ slightly, but both can be used with derived credentials.
While smart cards work well in traditional desktop and laptop environments, they aren't well adapted for mobile devices. Many government desktops and laptops have built in smart card readers, or if they don’t, users can plug in a USB smart card reader. This doesn’t work well on mobile devices. Although, smart card readers exist for mobile devices, the user experience is poor, readers are expensive, and they aren't exactly easy to carry around.
MobileIron to the rescue
MobileIron recognized the challenge our customers faced when complying with smart card and derived credential regulations in a mobile environment and created a solution to make the deployment of derived credentials easy. Working with trusted certificate and smartcard solutions like Entrust, DISA Purebred, Xtec, and Intercede, we created a derived credential solution that enables organizations to extend their existing security investments in smart cards to their mobile infrastructure. The solution supports government regulations and security standards such as Homeland Security Presidential Directive-12 (HSPD-12), OMB ICAM initiatives, FIPS 201, and NIST SP:800-157.
The MobileIron PIV-D manager solution integrates with Public Key Infrastructure (PKI) systems to seamlessly deploy derived credentials and manage the lifecycle of the credentials in any mobile enterprise or government organization. MobileIron PIV-D Manager stores the derived credentials securely in our encrypted MobileIron AppConnect framework, which is FIPS 140-2 enabled. The credentials can then be seamlessly shared with other secure AppConnect apps such as Email+, Docs@Work, Web@Work, and native mobile OS apps for secure single sign-on, and S/MIME use on iOS and Android devices.
MobileIron assisted government agencies such as the Federal Emergency Management Agency (FEMA) and the DoD’s Defense Information Systems Agency (DISA) to deploy derived credentials seamlessly. These agencies now have tens of thousands of devices leveraging derived credentials, enabling their end users to access enterprise resources securely from mobile devices using their device as their identity.
FEMA implemented derived credentials agency wide with the MobileIron PIV-D manager solution, enabling access to enterprise services and email from their mobile devices. FEMA disaster recovery personnel now use derived credentials on their mobile devices to seamlessly login into mission critical apps while eliminating usernames and passwords along the way.
What’s next?
While derived credentials provide a strong authentication mechanism backed by PKI, Zero Sign-On enables derived credentials for use with a comprehensive set of attributes before granting access to enterprise resources. MobileIron’s approach to mobile-centric, zero trust security significantly reduces risk by giving organizations complete control over enterprise data as it flows across devices, apps, networks, and cloud services.
If you want to learn more about MobileIron’s world class derived credential solution please contact us.
