Key Takeaways
- The CISA Known Exploited Vulnerabilities (KEV) list reached 925 entries. It is projected to exceed 1,000 by late August, indicating accelerating risk.
- Apple introduced Rapid Security Responses for iOS, iPadOS and macOS to deliver faster fixes.
- Microsoft released patches for 51 vulnerabilities, including six critical and three known exploited flaws, making May OS updates the top priority for Windows. Notable fixes address a secure boot bypass (CVE-2023-24932), a Win32k elevation of privilege issue (CVE-2023-29336), and a Windows OLE remote code execution (CVE-2023-29325) with high exploit risk.
- Mozilla delivered Firefox 113 and Firefox ESR 102.11 updates that resolve 13 CVEs, including several high severity bugs, completing the third party patch coverage for this cycle.

It’s Patch Tuesday once again. The CISA KEV database is now up to 925 CVEs and at the rate it’s increasing, it's likely we'll see it turn over the 1,000 mark around late August this year. Apple has released a new capability called Rapid Security Responses for iOS, iPad and MacOS. For systems running the latest version of each, they'll start receiving faster responses to security vulnerabilities, security improvements and mitigations. In general, the world is moving quickly toward a risk-based approach to security with the goal of taking faster action to reduce the most possible risk to your environment.
That's one of the key goals of Ivanti’s Patch Tuesday efforts. To provide quick analysis on what's released from Microsoft and other vendors, identify priorities from a risk perspective and give as much of a heads up as possible regarding changes and known issues that may impact your environment as you roll out the updates each month.
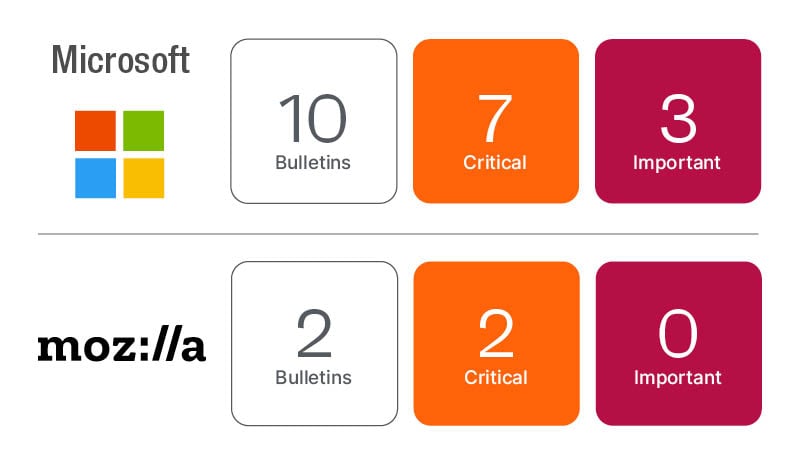
Microsoft updates
For May 9th, 2023, Microsoft has resolved 51 vulnerabilities, 13 of which were previously released and recently updated. There are three known exploited vulnerabilities resolved this month, one of which was previously released and recently updated. There's one additional publicly disclosed vulnerability that's reached proof-of-concept code maturity, meaning the risk of exploit is high. Six CVEs are rated as Critical, five affecting the Windows OS and one affecting Sharepoint.
The good news this month is all three known exploits and the public disclosure along with five of the six Critical CVEs will be resolved by pushing the Microsoft OS updates this month. That's going to be your highest priority on the Microsoft side.
Microsoft has resolved a Secure Feature Bypass vulnerability in Secure Boot (CVE-2023-24932). The vulnerability was reported by SentinelOne and ESET and has been confirmed to be exploited in the wild. The CVE is rated as Important by Microsoft’s assessment algorithms, but with the confirmed exploits you can ignore that severity rating and respond to the real-world risk indicators.
The vulnerability does require the attacker to have either physical access or administrative permissions on the target system, with which they can install an affected boot policy that'llbe able to bypass Secure Boot to further compromise the system. The vulnerability affects all currently supported versions of the Windows OS.
Microsoft has resolved a Win32k Elevation of Privilege vulnerability (CVE-2023-29336). The vulnerability was reported by analysts from Avast and has been detected in exploits in the wild. The CVE is rated as Important by Microsoft’s assessment algorithms, but with the confirmed exploits you can ignore that severity rating and respond to the real-world risk indicators. The exploit doesn't require user interaction and if exploited would give the attacker system-level privileges. The vulnerability affects Windows 10 and Server 2008 up to 2016.
Microsoft has resolved a Remote Code Execution vulnerability in Windows OLE (CVE-2023-29325). The vulnerability was reported by an analyst from Vul Labs. The CVE is rated as Critical and while it hasn't been detected in active exploits in the wild, it does have proof-of-concept level code samples and has been publicly disclosed, meaning the risk of exploit is high. The vulnerability can be exploited over the network and doesn'trequire user interaction, but can easily target a user to be exploited.
The vulnerability is in the Windows OS, but the Preview Pane in Outlook can be used as an attack vector. Microsoft has even recommended users read email messages in plain text format to mitigate the risk until you can get the update in place. There are other steps and a race condition to win for the attack to be successful, which gives the complexity to exploit as High and may reduce the possibility of this vulnerability being utilized in an attack.
Microsoft updated 13 CVEs this month. Most of the updates were only changes to CVSS or URL data in the CVE bulletins. The CVEs that were updated with more than an informational change are:
- CVE-2013-3900 – WinVerifyTrust Signature Validation vulnerability which has a long history and was updated in April 2023 as well. This vulnerability is known to be exploited. The update this month states that supporting code to resolve this vulnerability has been incorporated into all current Windows OS editions already (as of April 2023 Patch Tuesday release), but a registry key must be set to turn on enforcement.
- CVE-2022-26928 – Elevation of Privilege vulnerability in Windows OS. Originally released in September 2022. Microsoft expanded the affected products to include all currently supported versions of Windows OS. This will be taken care of as part of your OS updates this month.
Third party security updates
Mozilla has released security updates for Firefox and Firefox ESR, resolving 13 CVEs.
- Firefox 113 released resolving 13 CVEs, five of which were rated as high.
- Firefox ESR 102.11 released resolving eight CVEs, four of which are rated as high.
For more details from our graphic summary of this month's releases, read our blog post or register for the Ivanti Patch Tuesday webinar (live or on-demand) to get up to date analysis on priorities, known issues and other security news. Visit our Patch Tuesday page for more information.
