Key Takeaways
- Microsoft released 123 patches, including 18 Critical fixes. The updates target the wormable Windows DNS Server vulnerability (CVE‑2020‑1350), a Critical Servicing Stack Update (CVE‑2020‑1346), and prioritize OS, browser and Office components.
- Oracle’s quarterly CPU adds 11 Java SE fixes, 53 Fusion Middleware patches, and 40 MySQL updates. Many of these are remotely exploitable and have CVSS scores up to 9.8.
- Google Chrome’s latest update addresses 38 vulnerabilities, including a Critical fix.
- Adobe Creative Cloud Desktop adds a Critical fix for CVE‑2020‑9682. Both updates should be applied promptly.
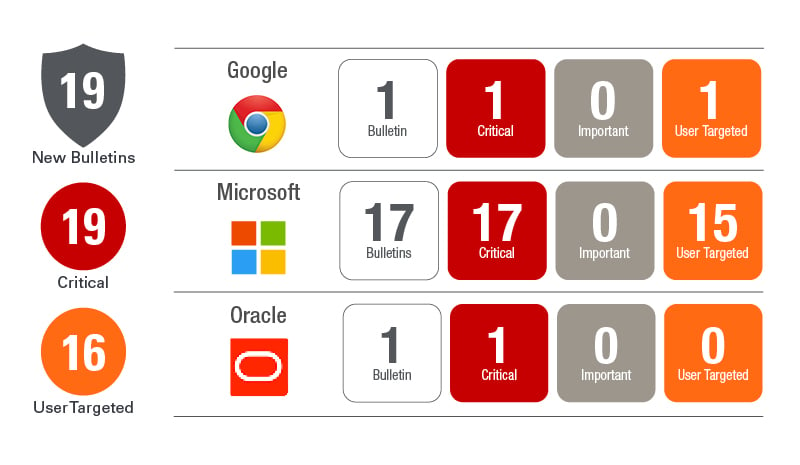
 This month we have the typical lineup from Microsoft with OS, browser and Office suite updates. Additional development components like ChakraCore, Visual Studio, Open Source Software, Azure DevOps, and .Net Framework are also included. In total Microsoft has resolved 123 unique vulnerabilities, 18 of which are rated as Critical. There is one publicly exploited vulnerability (CVE-2020-1463) and a particularly nasty critical vulnerability in Windows DNS Server (CVE-2020-1350) that warrants some immediate attention.
This month we have the typical lineup from Microsoft with OS, browser and Office suite updates. Additional development components like ChakraCore, Visual Studio, Open Source Software, Azure DevOps, and .Net Framework are also included. In total Microsoft has resolved 123 unique vulnerabilities, 18 of which are rated as Critical. There is one publicly exploited vulnerability (CVE-2020-1463) and a particularly nasty critical vulnerability in Windows DNS Server (CVE-2020-1350) that warrants some immediate attention.
Microsoft has also included Servicing Stack Updates (SSUs) for all Windows versions in this month’s updates that resolves a critical vulnerability, which is a first. CVE-2020-1346 is an Elevation of Privilege vulnerability in Windows Modules Installer that could allow an attacker to gain elevated privileges on the affected system. In this case the attacker would need to execute code on the target system. This vulnerability affects all Windows OSs including Windows 7, Server 2008 and 2008 R2.
Windows DNS Server has a Critical vulnerability (CVE-2020-1350) which is worm-able. This means an attacker could exploit this vulnerability remotely without authentication and it can spread very quickly to all DNS Servers in your environment. The CVE carries a CVSS base score of 10.0 and Microsoft has provided some strong guidance on responding to this one. In a blog from the MSRC today they urge those who cannot quickly deploy the update to use a registry-based workaround to mitigate the issue until you can get the update deployed. The workaround does NOT require restarting the system.
This month’s publicly disclosed vulnerability (CVE-2020-1463) is also an Elevation of Privilege. In this case it is a vulnerability in Windows SharedStream Library, affecting Windows 10 and Server 2016 and later. The vulnerability could allow an attacker to execute code with elevated permissions. The attacker would need to be locally authenticated to exploit this vulnerability.
The 18 Critical CVEs affect the Windows OS, IE, Office, SharePoint, .Net Framework and Visual Studio. OS, browser and Office should be prioritized highest, but SharePoint, .Net and Visual Studio should not be neglected.
Oracle has pre-announced their quarterly CPU for today as well. This often drops later in the evening, but here are the highlights. Oracle Java SE is going to resolve 11 vulnerabilities all of which are remotely exploitable without authentication. Highest CVSS v3.1 base score is 8.3. Fusion Middleware is resolving 53 CVEs, 49 of which may be remotely exploited without authentication. Highest CVSS v3.1 base score is 9.8. MySQL is resolving 40 vulnerabilities, six of which may be remotely exploited without authentication. Highest CVSS v3.1 base score is 9.8.
For more details on the Oracle release today take a look at their pre-release announcement here.
Adobe released five bulletins today, but only one included a Critical vulnerability. Adobe Creative Cloud Desktop Application resolved four CVEs including CVE-2020-9682, which was rated as Critical. Flash Player did release today, but no CVEs were reported in this release.
Google also decided to join the party with a Google Chrome update resolving 38 vulnerabilities including at least one Critical and many High CVEs. Chrome 84.0.4147.89
From a third party perspective you should look to update Chrome and Java as high priority items this month.
