Key Takeaways
- Microsoft shipped 14 patches fixing 55 vulnerabilities and added full Speculative Store Bypass (SSBD) support for all Intel‑based Windows systems while working with AMD on the same mitigation.
- Two publicly disclosed Windows elevation‑of‑privilege flaws (CVE‑2018‑8313, CVE‑2018‑8314) affect most OS versions. Ivanti recommends prioritizing OS and IE updates, including CVE‑2018‑8282 and the PowerShell Editor Services vulnerability (CVE‑2018‑8327).
- Adobe Flash, Acrobat/Reader, and Apple iTunes/iCloud received updates fixing numerous critical bugs. Oracle’s July CPU release will bring Java patches. You should deploy these updates quickly, otherwise mitigate exposure by restricting access, adding layered protections.
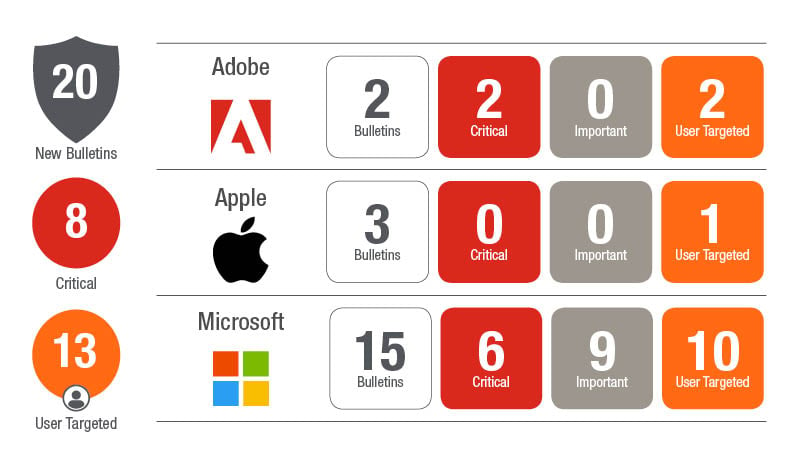
Microsoft has released 14 updates today, resolving 55 distinct vulnerabilities including three publicly disclosed vulnerabilities. Microsoft also updated ADV180002 and ADV180012 regarding Meltdown and Spectre variants. ADV180002 looks like it just received some housekeeping so for variants 1 (CVE-2017-5753), 2 (CVE-2017-5715), and 3 (CVE-2017-5754) there are no updates other than documentation cleanup. ADV180012 was updated to state that variant 4 (CVE-2018-3639) for Speculative Store Bypass is updated on all supported Windows systems for Intel processors and that Microsoft is working with AMD to close the loop on AMD processor exposure to variant 4.
As of July 10, 2018, updates are available for all systems with Intel processors. Microsoft is working with AMD to assess the availability and readiness of SSBD in supported versions of Windows. See the Recommended actions section for information about the updates and the steps to apply to turn on SSBD.
There are two publicly disclosed vulnerabilities in the Windows OS this month. CVE-2018-8313 and CVE-2018-8314 are Elevation of Privilege vulnerabilities that affect the majority of the Windows OSs. 8313 affects all but Win 7 and 8314 affects all but Server 2016.
The third public disclosure is a spoofing vulnerability in the Edge browser in how it handles specific HTML content. This could allow an attacker to impersonate a legitimate website and trick a user into believing it is the legitimate website.
Ivanti Prioritization:
Microsoft OS Updates: Between the two public disclosures, CVE-2018-8282 (Elevation of Privilege) which can allow an attacker to run arbitrary code in kernel mode, and vulnerabilities like CVE-2018-8287, CVE-2018-8288 and CVE-2018-8296, which allow an attacker to embed ActiveX controls marked “safe for initialization” into an office document hosting the browser rendering engine or to host it in a compromised website, you pretty much should plan on updating OS and IE this month. Aside from the Elevation of Privilege vulnerabilities, several of the others could be mitigated by running as less than a full admin.
Another interesting vulnerability this month is CVE-2018-8327, which allows an attacker to execute malicious code in a PowerShell Editor Services Process. This is a type of vulnerability that gives a Threat Actor a lot of flexibility to further compromise a system using fileless attack methods.
.Net Framework received an update today resolving several Important CVEs. While a little more difficult to exploit, an attacker can possibly bypass certificate validation, allowing for expired certificates to be accepted and unauthorized components to be presented to .Net applications or take control of an affected system if they pass certain input to a susceptible .Net method. While this is not extremely urgent, the .Net update should be tested and rolled out in a reasonable timeframe.
On the non-Microsoft front there are a number of third party updates this month that warrant some attention.
Adobe Flash released today resolving two vulnerabilities, one of which is critical. Adobe Acrobat and Reader, released today as well, resolving over 104 vulnerabilities. About half or better are critical. Yeah, patch those! Flash is still one of the most highly targeted applications and poses a significant risk to your environment and should pretty much be patched ASAP when an update is available or removed altogether from the environment. Adobe Reader and Acrobat are also highly targeted and that is a lot of vulnerabilities. Our recommendation – get both rolled out quickly.
Apple released updates for iTunes and iCloud that resolved more than 10 vulnerabilities each.
Oracle will be releasing the July Quarterly CPU on Tuesday the 17th, so watch for a variety of updates from Oracle including Java! Looking back at the April Java update as an indicator, it resolved 14 vulnerabilities, 12 of which were remotely exploitable over the network. Three of those were rated as an 8.3 CVSS score. Java may not get as many Zero Days as it once did, but it is still a common target because attackers know it often goes unpatched. If you cannot patch it, you need to lock the system down in a number of other ways. Don’t allow direct Internet connectivity; limit access to only specific users; and add additional layers of protection on the system and tighter policies to protect what is low-hanging fruit to attackers.
As always tune into Ivanti’s Patch Tuesday landing page for updated analysis and sign up for our monthly Patch Tuesday webinar.
