Key Takeaways
- Organizations must continue Log4j remediation by running vendor‑provided scanners. Apply updates to version 2.17.1 (Java 8), 2.12.4 (Java 7) or 2.3.2 (Java 6) to address all known CVEs.
- A date format bug in the on premises Exchange Transport service caused email queues to stall. Microsoft’s script and service restart instructions should be applied after disabling the temporary antimalware workaround.
- January’s patch batch includes 97 Microsoft CVEs (nine critical) covering Windows OS, Edge, .NET, Exchange, O365, Defender and Dynamics.
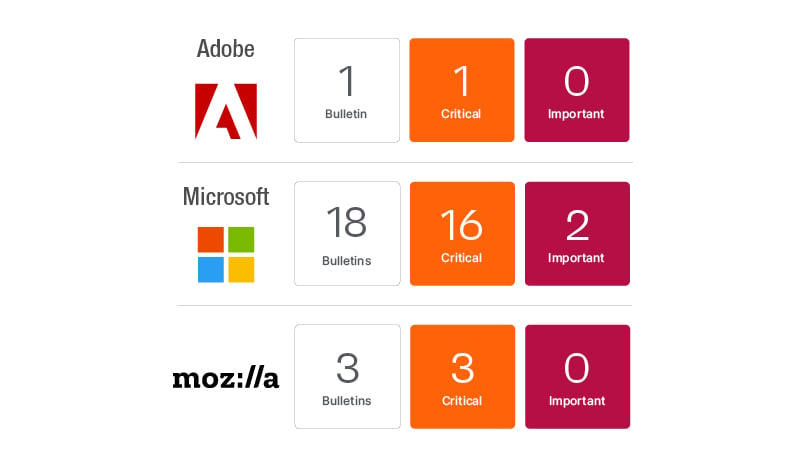
- Adobe released five updates for 41 CVEs (22 critical) and Mozilla three updates for 18 CVEs (nine critical). Oracle’s quarterly CPU will follow on Jan 18.
Get your snow shovels out, bundle up and prepare for Patch Tuesday January 2022! Sorry for my Minnesota winter humor there, but I felt it was a good metaphor for what to expect this month.
There is a healthy lineup of issues to investigate this month including Log4j cleanup activities continuing in many organizations, a script to fix a date value limitation in on-premises Microsoft Exchange Transport service that caused email to become stuck for many organizations, and security updates from Microsoft, Adobe, Mozilla and Oracle (releasing on January 18, 2022).
Log4j cleanup is still ongoing for many organizations
For most the question of if they have caught all possible instances of Log4j is really the biggest question. As I discussed in a blog post on Patch Tuesday December 2021 the Log4j vulnerabilities were not something you could resolve with a simple update. It is a messaging component built into a variety of web services and vendor applications. It was difficult to detect in many cases, so code scanners and network vulnerability scanners struggled to accurately identify exposure. Organizations that were able to respond quickly found that truly understanding their exposure required rolling up their sleeves. They quickly assessed their internal development teams for use of Log4j and their vendor risk management process to determine what vendors they were consuming solutions from and assessing each to determine if they were exposed. As an additional step, security teams also utilized a variety of custom scanners purpose-built to scan for the Log4j binaries. This is crucial given Log4j was buried many cases in a few layers of JAR files which was throwing many vulnerability scanners off. Here is the latest guidance on Log4j for vendors and affected organizations:
- Organizations: Determine whether your products with Log4j are vulnerable:
- Consult vulnerable apps list and run Log4j scanner. CISA provides their list and scanner links, but there are others available as well. You should look to your list of vendors and compare with the list of vendors in lists like the CISA vulnerable apps list. If you have vendors on your list not captured it is recommended to seek guidance directly from vendors to ensure there is no exposure.
- Run Log4j scanner: This is in addition to vulnerability scanners you normally utilize to ensure you are catching the cases that are causing vulnerability scanners to potentially miss detection.
- Remediate detected instances of Log4j using vendor supplied mitigation or updates that have been made available.
-
Vendors and development teams: Review Apache Log4j security vulnerabilities page as there are now multiple Log4j vulnerabilities being tracked. ISA urges users and administrators to upgrade to Log4j 2.17.1 (Java 8), 2.12.4 (Java 7) and 2.3.2 (Java 6) to resolve all currently known vulnerabilities including those with known exploits (original Log4Shell exploit CVE-2021-44228 and the additional fix to resolve non-default configurations CVE-2021-45046). The additional vulnerabilities that have been resolved (CVE-2021-45105 and CVE-2021-45046) have been resolved in the latest releases. While there are no known exploits for these two additional CVEs, there is an elevated risk of potential exploit so best not to let these linger too long.
Microsoft Exchange NYE’s Surprise
Microsoft Exchange administrators got a new year’s surprise as on-premises Exchange servers started experiencing email becoming stuck as queues ran into a date format issue in the Filtering Management Service. Guidance quickly became available on January 1, 2022 as email stuck in transport queues quickly got backed up. Initial guidance was to disable the antimalware service as a workaround to get email flowing again. Guidance was later updated with scripted and manual steps to stop the affected services and update the affected engine and restart services resolving the issue. If you still have the initial mitigation in place it is recommended to take the additional steps Microsoft has provided to implement the amupdate and restart the transport service.
January Patch Tuesday 2022 includes updates from Adobe, Microsoft and Mozilla
Keep in mind the Oracle Quarterly CPU will be coming on Tuesday January 18, so don’t lose sight of that in your update schedules in the next few weeks.
Adobe has released 5 updates resolving a total of 41 CVEs, 22 of which are rated as Critical. The Acrobat and Reader update is rated as priority 2, with updates for Illustrator, Bridge, InCopy, and InDesign rated as priority 3.
Mozilla has released 3 updates resolving a total of 18 unique CVEs this month, 9 of which are rated as Critical. The updates affect Mozilla Thunderbird, Firefox and Firefox ESR and all three are rated as High severity.
Microsoft has released updates resolving 97 unique CVEs, 9 of which are rated as Critical. There are 6 publicly disclosed vulnerabilities this month, but no Zero Days. The Microsoft updates include the Windows OS, Edge (Chromium), .Net Framework, Microsoft Exchange, O365, Defender, and Dynamics. While there are no known exploited vulnerabilities this month, the six publicly disclosed vulnerabilities may warrant more immediate attention as they could have exposed proof-of-concept code or other details that can give adversaries additional details to develop an exploit. This month’s Windows OS updates include fixes for all of the publicly disclosed vulnerabilities.
Microsoft has resolved a Denial of Service vulnerability in Windows Event Tracing Discretionary Access Control List (CVE-2022-21839) affecting Windows 10 1809 and Server 2019 versions of the Windows OS. The DoS vulnerability does have a Proof-of-concept and has been confirmed.
Microsoft has resolved a Spoofing vulnerability in Windows Certificates (CVE-2022-21836) affecting Windows 7 and server 2008 and later versions of the Windows OS. This vulnerability allows an attacker to bypass the WPBT binary verification by using a small number of compromised certificates. Microsoft has added those certificates to the Windows kernel driver block list, driver.stl. Certificates on the driver.stl will be blocked even if present in the Windows Platform Binary Table (WPBT). The Spoofing vulnerability does have a Proof-of-concept and has been confirmed.
Microsoft has resolved an Elevation of Privilege vulnerability in Windows User Profile Service (CVE-2022-21919) affecting Windows 7 and server 2008 and later versions of the Windows OS. The Elevation of Privilege vulnerability does have a Proof-of-concept and has been confirmed.
Microsoft has resolved a Remote Code Execution vulnerability in Windows Security Center API (CVE-2022-21874) affecting Windows 10 and Server 2016 and later versions of the Windows OS. The vulnerability has been confirmed, but no proof-of-concept code is available.
Microsoft has resolved a Remote Code Execution vulnerability in Libarchive (CVE-2021-36976) affecting Windows 10 and Server 2019 and later versions of the Windows OS. The open source library includes additional fixes for vulnerabilities dating back to 2006.
Microsoft has resolved a Remote Code Execution vulnerability in Open Source Curl (CVE-2021-22947) affecting Windows 10 and Server 2019 and later versions of the Windows OS. The open source library includes additional fixes for vulnerabilities dating back to 2000.
