Key Takeaways
- Microsoft released 47 updates, including seven critical fixes for Windows 10, Server 2019, Chakra Core, and Edge. A publicly disclosed Important flaw in the Jet Database Engine (CVE‑2019‑0579) could allow remote code execution.
- Install the Windows 10 1703 January servicing stack update and confirm that the December out of band Internet Explorer patch (CVE‑2018‑8653) is present via the cumulative update or the IE update. Skipping these patches may block future updates and leave systems vulnerable to script based attacks.
- Adobe delivered a critical Acrobat and Reader update, while its Flash Player release contained no security fixes. Oracle’s January CPU ends public updates for Java SE 8, so environments should migrate to JDK 11 and retire legacy JREs.
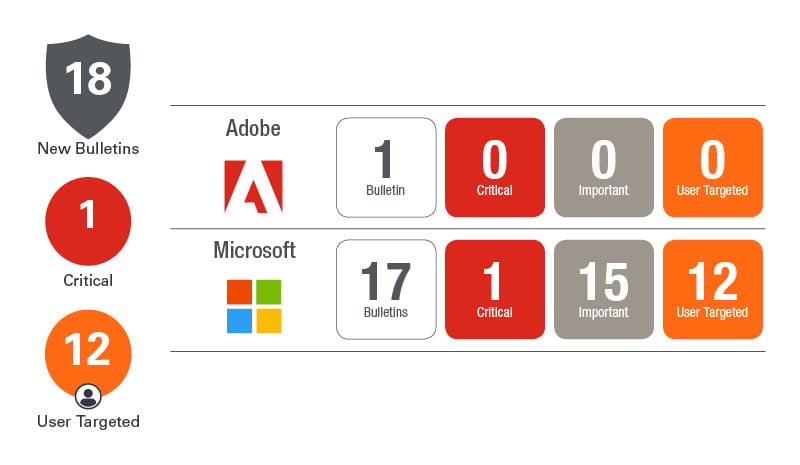
January Patch Tuesday looks like a mild one. Microsoft has released updates for the Windows operating system, Internet Explorer, Edge, Office, Sharepoint, .Net Framework and Exchange. Microsoft resolved a total of 47 unique vulnerabilities and most are only rated as Important. Only seven of the CVEs resolved are rated as Critical and those are all on Windows 10 and Server 2019 as well as Chakra Core and the Edge browser.
There is one publicly disclosed vulnerability this month and that is CVE-2019-0579, which affects all of the Windows operating systems, but is only rated as Important. The vulnerability is in the Jet Database Engine and could allow an attacker to execute code remotely on a victim’s system by enticing the victim to open a specially crafted file. While only rated as Important, this vulnerability has been disclosed, meaning enough information was released to the public that an attacker could have an easier time to develop exploits for the vulnerability. Public disclosure increases the likelihood that this vulnerability could be exploited.
Microsoft has released an updated servicing stack for Windows 10 1703. This is the only servicing stack update this month. Servicing stack updates update the update system…. Err if that makes any sense. In other words, if you don’t do this update you may not be able to reliably conduct future updates amongst other changes to the system. Servicing stack updates are in addition to the cumulative updates. Read here for all you ever wanted to know about Servicing stack updates.
On the Microsoft side, the thing you should be concerned about is whether you addressed the Internet Explorer out-of-band that occurred in December. On December 19 Microsoft released an emergency patch to resolve a zero-day vulnerability in Internet Explorer’s scripting engine. The Jscript vulnerability (CVE-2018-8653) allows an attacker to leverage the scripting engine within IE by simply viewing a malicious website. Once successful, the attacker can gain control of the system with the user’s rights.
So if you did the December Patch Tuesday updates, but did not catch the out-of-band, you will want to ensure all of your Windows systems get either the January cumulative update or the IE update as quickly as possible.
Outside of Microsoft there isn’t a whole lot more going on just yet. Adobe released an update last week for Adobe Acrobat and Reader (APSB19-02),
which resolved two critical vulnerabilities. Adobe Flash Player released today but did NOT include any security updates. If you are up to December’s APSB18-42 release you should be set there.
January is Oracle’s quarterly CPU cycle so next week on the 15th you can expect all of your favorite Oracle software to receive some critical patch updates. I highly suggest you read up on the Java support changes going forward. Java SE 8 is receiving its last public update. After this one you would need to subscribe to Oracle’s update program for Java 8 or upgrade to Java 11 JDK. For more details see my writeup from last week’s Patch Tuesday Forecast.
On September 17, 2018 Oracle Announced Java SE 8 End of Public Updates set for January 2019. The upgrade path for Java SE 8 was previously to upgrade to Java SE 10, but that EOL’ed in late September 2018 as well. So the new path is to upgrade to Java JDK 11. Yes, JDK. Why? Because there really isn’t a separate JRE any longer and this is where many companies are currently left scratching their heads. The Java Runtime is no longer packaged separately.
In JDK 11 the software developers are supposed to package up only the necessary modules for their specific application using jlink or jmod. In short, this will change the way you distribute your Java applications. For many companies the details are still a bit foggy. As a patch administrator your biggest concerns should be:
- How long before you can remove legacy Java JREs from your environment? They will become a security liability over time. Software obsolescence is the cause of many security incidents. It is also a really fun word.
- Under this new model how will security vulnerabilities be identified and how quickly will development teams be turning out updates? Then how will that update be distributed?
Stay informed by visiting Ivanti’s Patch Tuesday landing page for updated analysis and sign up for our monthly Patch Tuesday webinar.
