Key Takeaways
- Microsoft released a light Patch Tuesday with 49 new CVEs and seven expanded CVEs, including two critical OS vulnerabilities that should be prioritized in testing.
- The update set also includes Chrome, Firefox, Thunderbird, Edge and an Oracle quarterly CPU release on Jan 16 that will trigger updates across many Java runtimes.
- Organizations should shift to a priority update process that fast tracks zero day or exploited fixes and align CIO and CISO leadership around risk focused remediation.
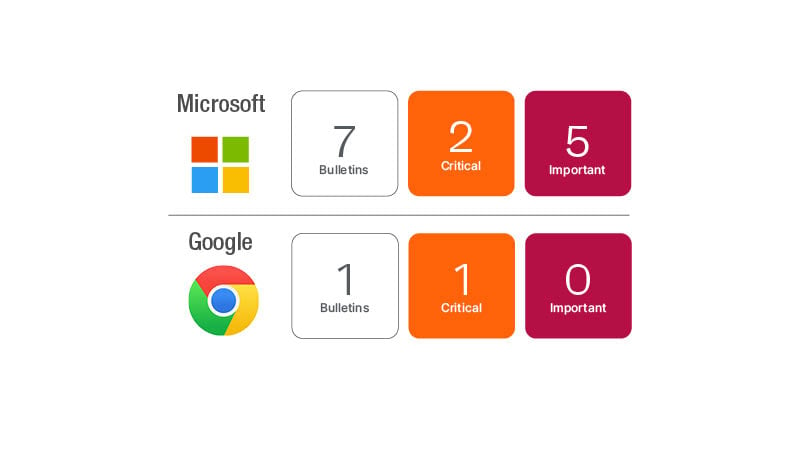
Easing into 2024 with a light lineup from Microsoft and third-party updates from Google and Mozilla, and you can also expect a quarterly update from Oracle next week. Microsoft has resolved 49 new CVEs and seven CVEs from 2023 to expand the affected products to include additional updates. No public disclosures or exploited reports at this time, so business as usual. The two critical CVEs in the OS update this month are the highest risk. Get things evaluated and tested as part of your normal maintenance schedule.
This month’s updates affect the Windows OS, Office 365 and SharePoint, .Net Framework, SQL Server and Visual Studio.
Updates to Google Chrome, Mozilla Firefox and Thunderbird, and the Microsoft Edge Chromium browser are included in the lineup of updates.
Keep an eye out for Oracle’s quarterly CPU release coming on Tuesday, January 16th. This will include many Oracle updates, but will also kick off the domino effect on all of the Java frameworks like RedHat OpenJDK, Amazon Corretto, Azul Zulu, Eclipse Adoptium, Adopt OpenJDK and others.
The seven CVEs that were updated this month affect multiple Microsoft Visual Studio editions. CVE-2023-29356, CVE-2023-32025, CVE-2023-32026, CVE-2023-32027, CVE-2023-32028, CVE-2023-29349 and CVE-2023-36042 will potentially surprise some folks by popping up in vulnerability scans this month. The CVEs were expanded to include the Visual Studio version as affected.
Shifting your vulnerability remediation strategy in 2024
Looking ahead to 2024, most organizations have adopted a monthly maintenance and a priority updates remediation strategy. This offers a lot of advantages but does require some capabilities to be effective. The biggest value is shifting your organization’s conversation from the cumbersome and boring topic of patching to one of reducing vulnerability exposure. It may not seem like a huge difference for those of you who are running on the continuous remediation treadmill, but from a business perspective, think about the way this frames the conversation.
Advantages
- Don’t try to tackle the sheer mass of updates. Focus on risk to the business and mitigate that risk quickly. This shifts the conversation and even the KPIs you are measuring over to being very risk-focused.
- Establish a priority update track with a lighter process, but strict rules for including an update. Timeframe ranges based on how aggressive an organization wants to get. Organizations adopting this priority update track are adding a weekly to daily remediation schedule to their remediation process.
- Establish well-defined criteria to set boundaries and reduce the need for a heavy approval process or oversight. An update can only fall into the priority update track if it includes a zero-day vulnerability or known exploited vulnerability.
- With this shift in strategy, you have effectively shortened the exposure time to your organization to days or even hours, versus weeks to a month or more.
Requirements
- Executive alignment on buying, especially between the CIO and CISO roles within the organization.
- Business-wide accountability. IT and Security may execute the day-to-day activities, but business line owners are accountable and responsible for vulnerability remediation for their areas.
- Clear and well-defined outcomes and KPIs to measure success, including accountability. Reporting at multiple levels, including organization-wide and by business unit, service or region (depending on organization).
- The right tools to manage the end-to-end process, including vulnerability scanning, risk intelligence, prioritization, exception handling and workflows for patch remediation, integration into DevOps tools and routing of additional tickets to correct teams, etc.
