Key Takeaways
- Two exploited zero‑day flaws were patched. One is an IE memory‑handling issue (CVE‑2018‑8373) affecting all Windows versions.
- The other is a Windows Shell path‑validation bug (CVE‑2018‑8414) on recent Windows 10 and Server builds. Apply these updates first.
- Microsoft’s Advisory 180018 addresses the L1TF (Foreshadow) variant of Spectre/Meltdown.
- It requires OS and firmware updates. It also recommends disabling hyper‑threading as a temporary mitigation.
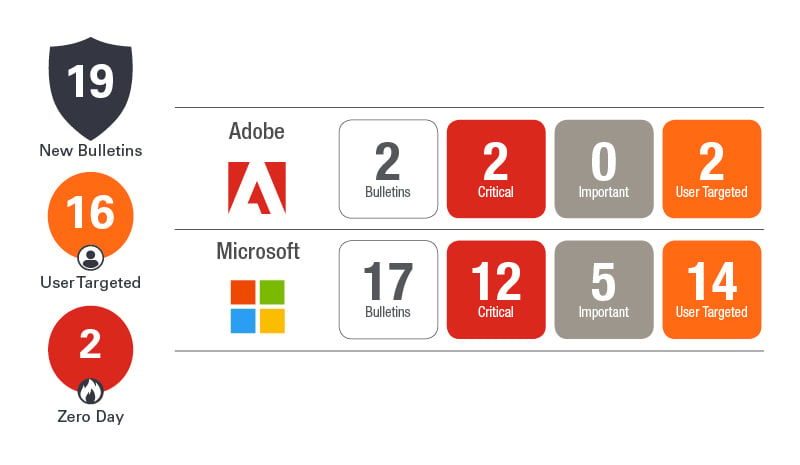
The updates continued to flow today despite this being the time for summer vacations. Microsoft has released 17 updates today resolving 60 distinct vulnerabilities, and Adobe released security updates for several of their products. After two Patch Tuesdays with no zero-day vulnerabilities reported, we get two this month. Spectre and Meltdown continue to haunt us as well. So let’s dig into these recent releases.
The two zero-day vulnerabilities are CVE-2018-8373 and CVE-2018-8414. Both are publicly disclosed and exploited. CVE-2018-8373 is a vulnerability that exists in the way that the scripting engine handles objects in memory in Internet Explorer. Exploitation could result in remote code execution and grants the same privileges as the logged-in user including administrative rights. Because this vulnerability exists in IE 9, 10, and 11, it affects all Windows operating systems from Server 2008 to Windows 10. The second zero-day vulnerability, CVE-2018-8414, is a code execution vulnerability that exists when the Windows Shell does not properly validate file paths. Exploitation can also result in remote code execution with the privileges of the logged-in user. This vulnerability is not as widespread, existing on only Windows 10 1703 and newer, Server 1709 and Server 1803. Now that the fixes are available, and given there are known exploits, you should give these fixes top priority this month.
Microsoft also issued Advisory 180018 regarding a new Meltdown and Spectre variant. This advisory, Microsoft Guidance to mitigate L1TF variant, addresses three vulnerabilities – CVE-2018-3615, CVE-2018-3620, and CVE-2018-3646. According to Microsoft, “Speculative execution side-channel vulnerabilities such as L1 Terminal Fault (L1TF) can be used to read the content of memory across a trusted boundary and if exploited, can lead to information disclosure.” Correcting these vulnerabilities requires both a software and firmware (microcode) update. As a temporary mitigation, Microsoft does recommend disabling Hyper-threading which can have a major performance impact. Like the previous guidance around these vulnerability variants, management and remediation is time-consuming and tedious. Read the Advisory carefully before you take action and test your non-production systems before proceeding. Incidentally, this variant is also known by the code name Foreshadow. If you are looking for more information, check out this Usenix page for a detailed explanation.
Microsoft released updates for many of their products this month. Of special note, there are new updates for .NET which interestingly only fix one vulnerability. The release of .NET caused a number of stability problems last month, so suspect a number of fixes besides the base security vulnerability are included. Test carefully before applying on production machines. Microsoft continues the variety with a critical vulnerability in SQL 2016 and 2017. Exchange was also patched with updates to Exchange 2010, 2013, and 2016 covering 2 CVEs. Visual Studio 2015 and 2017 round out the group with a single CVE.
In our July blog, we mentioned that Oracle was releasing their quarterly Critical Patch Update (CPU) on July 17th. Make sure you take a look at their Advisory providing the latest updates including those for Java. Oracle also provided a rare out-of-band Advisory on August 10th to address CVE-2018-3110. With a CVSS v3 base score of 9.9, this vulnerability is easy to exploit and can provide direct shell access to your database. If you are using Oracle database versions 11.2.0.4 or 12.2.0.1 on Windows, we strongly recommend you apply this latest patch soon. Note that updates for any version on Linux and Windows 12.1.0.2 were provided in the July CPU. This new advisory is for previous versions of the database.
After the large volume of non-Microsoft security releases in late July and earlier this month, we should have expected more Adobe updates. Flash Player, as usual, was updated to fix five vulnerabilities. However, after 104 vulnerabilities were addressed in a scheduled update last month, we didn’t expect another Reader and Acrobat update fixing two new critical vulnerabilities. There were updates for Creative Cloud and other Adobe products, so please revisit your Adobe patch routine this month.
This busy patch cycle continues. Take a close look at all the third party and Microsoft security updates that were recently released and plan accordingly. There is lots of work ahead.
