July Patch Tuesday 2017
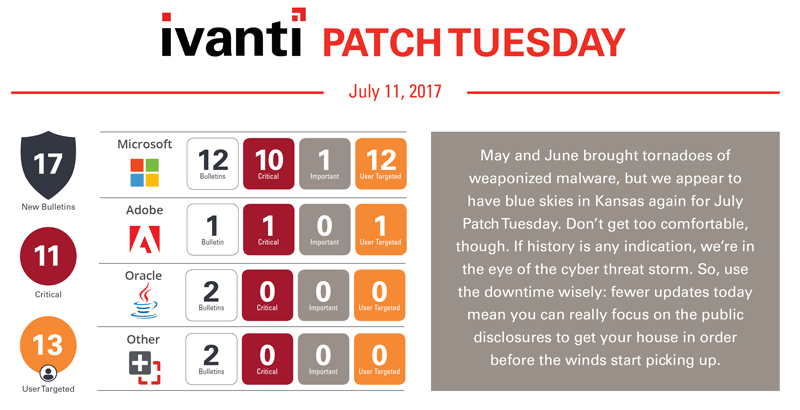
After the first half of the year July’s Patch Tuesday seems a little boring. There are a couple of things of interest, but overall, a pretty light round of updates. Depending on how you count them, there are 12 updates from Microsoft this month. Ten of the updates are rated as critical and one as important. We also have a moderate update for Exchange this month which has some interesting applicability notes to talk about. There were no zero days this month and also no updates released for XP or Server 2003, but there are four public disclosures to be aware of.
Be sure to check out all of Ivanti’s patch products:
Patch for SCCM
Patch for Windows
Patch for Linux, UNIX, Mac
Patch for Endpoint Manager
As expected, we also have an update from Adobe for Flash Player and Oracle will have their quarterly CPU, but that will actually drop next week on July 18. Just don’t forget about it.
All of the OS updates this month include some critical fixes and a few public disclosures, so regardless of if you are pushing the monthly rollup or the security-only bundle with Internet Explorer, they are all pretty much the same urgency. Let’s focus on the disclosures identified this month. A public disclosure is a vulnerability where enough information has been disclosed publicly for an attacker to have a jump start on building an exploit. In other words, the risk on a update that includes public disclosures is higher than another update of the same severity.
CVE-2017-8584 – Vulnerability in HoloLens which could allow remote code execution. This vulnerability affects Windows 10 1607 and Server 2016 and could allow an attacker to send a specially crafted wifi packet and take control of an affected system.
CVE-2017-8587 – Vulnerability in Windows Explorer which could allow a denial of service attack. This vulnerability affects Windows 7 up to Windows 10 1511 and Server 2008 up to Server 2012 R2 and how Windows Explorer attempts to open a non-existent file. This vulnerability could target a user by hosting a specially crafted website containing the reference to the non-existing file which would cause the users system to stop responding.
CVE-2017-8602 – Vulnerability in Internet Explorer 11 and Edge browsers parsing of HTTP content which could allow for a spoofing attack. The attacker could trick a user by redirecting them to a specially crafted website which could spoof content or serve as a pivot to chain an attack with other web services exploits. Attacks are user targeted and could take the form of phishing or watering hole attacks.
CVE-2017-8611 – Vulnerability in Microsoft Edge browser parsing of HTTP content which could allow for a spoofing attack. The attacker could trick a user by redirecting them to a specially crafted website which could spoof content or serve as a pivot to chain an attack with other web services exploits. Attacks are user targeted and could take the form of phishing or watering hole attacks.
The Exchange update this month applies only in specific circumstances. This update applies only if you are on the following:
- Microsoft Exchange Server 2013 SP1
- Microsoft Exchange Server 2013 CU 16
- Microsoft Exchange Server 2016 CU 5
If you have deployed the recently released 2013 CU 17 or 2016 CU 6 or happen to be on an earlier CU than either, the update will not apply. The update is rated as moderate, so a little less urgent.
Adobe Flash Player resolves three vulnerabilities this month. One of these is rated as critical and could allow remote code execution. Most importantly, you may need to update multiple instances of Flash on a system to fully resolve these vulnerabilities. There is the Flash Player install itself and if you have plug-ins for IE, Chrome or Firefox, those need to be updated as well. Some systems could have all four installed and in need of updates.
July is the Oracle CPU so keep an eye out next week for many critical updates from Oracle including Java JRE and JDK. This will drop on Tuesday, July 18.
For more details you can check out our Patch Tuesday analysis and join us for our monthly Ivanti Patch Tuesday Webinar to get more details on the updates, what to prioritize, issues to look out for and more.
