Key Takeaways
- April’s Patch Tuesday includes 65 fixes but no zero day exploits. Multiple critical vulnerabilities remain in Windows, Internet Explorer, Edge, and Office.
- The CVE-2018-1038 elevation of privilege flaw must be patched on Windows 7 and Server 2008 R2 x64 systems by installing KB4100480. The Malware Protection Engine should be updated to definition version 1.1.14700.5.
- Adobe released a Flash Player update that resolves three critical and three important vulnerabilities. Oracle’s quarterly Critical Patch Update, due April 17, will include Java patches that should be deployed promptly.
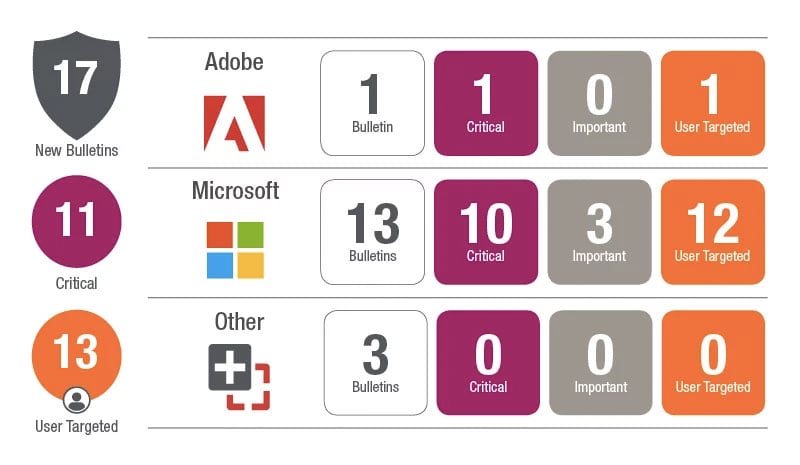
Microsoft has released updates today including 65 vulnerability fixes. While there are no Zero Day exploits in the April patch release, there were a couple of Zero Days identified between March and April Patch Tuesdays, which we will mention in a moment. There is one public disclosure this month in SharePoint Server. The challenging aspect of this month is that there are enough critical vulnerabilities in the Operating System, browser updates, and in Office that all three should be prioritized.
While the CVE-2018-1038 vulnerability was identified between March and April Patch Tuesday’s, it should be a top priority for anyone who has Windows 7 for x64-based Systems or Windows Server 2008 R2 for x64-based Systems. If you have installed any of the servicing updates released during or after January 2018, you need to install 4100480 immediately to be protected from this Elevation of Privilege vulnerability.
Microsoft also released an update to the Malware Protection Engine that resolved a remote code execution vulnerability that was identified. The fix for this is simply to update to the latest definitions. For the majority of environments using Microsoft’s Malware Protection Engine, this would have happened automatically. In the article, they identify the minimum definition version needed to resolve this issue, which is Version 1.1.14700.5.
There are multiple critical vulnerabilities in the Windows Operating System, Internet Explorer and Edge browsers, and on Office this month. There are a few critical kernel vulnerabilities resolved, several Microsoft graphics and TrueType font driver vulnerabilities resolved and a host of critical browser vulnerabilities resolved.
Microsoft has lifted the AV compliance key from the rest of the Windows OS updates in all but some vaguely mentioned edge cases. If you recall, the introduction of the Meltdown\Spectre mitigation updates caused a number of blue screens on systems running AV engines that were interacting with the kernel in unexpected ways. Microsoft introduced this key to prevent the blue screen scenarios from occurring, but required customers to jump through hoops if their AV vendor did not apply the key or if they were not running AV on a system. That restriction is now fully removed.
On the non-Microsoft front Adobe has released several updates today including an update for Adobe Flash Player. The Flash update resolves three critical vulnerabilities and three important vulnerabilities. Adobe Flash Player can show up in many forms on a single system. It can be installed on the system and as a plug-in in the major browsers, so to fully plug these vulnerabilities you may need to apply multiple updates on a single system.
Oracle is going to be releasing their quarterly Critical Patch Update next week on Tuesday, April 17th. Expect an update for Java. We strongly urge rolling out Java updates as they release. Java may not be as highly targeted as it once was, but it is still a low-hanging fruit target for Threat Actors. The recent SamSam Ransomware attacks are good examples. SamSam is able to exploit a variety of software vulnerabilities including some in Java. Attackers know that Java is one of those products that lags behind updates, leaving a number of exploits open.
As always tune into Ivanti’s Patch Tuesday landing page for updated analysis and sign up for our monthly Patch Tuesday webinar.
